By Laser 1 Technologies
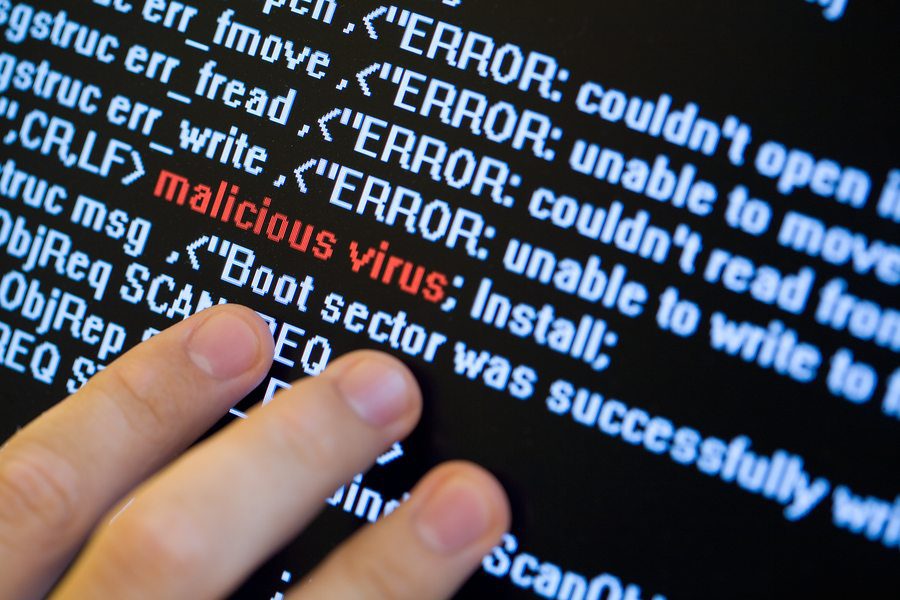
Smart Machines Are Vulnerable Machines
“Should you worry about intellectual property cybertheft?” was the question posed here on December 19, 2016. The answer is “yes.”
Cybertheft isn’t the only problem. Cyber attacks are also on the rise, largely enabled by the escalating dominance of the Internet of Things, the Industrial Internet of Things and Industry 4.0.
The Internet of Things has crept into our lives, earning an uneasy trust in exchange for the convenience it brings. As computing power increases and technology gets cheaper, networks connect more devices. With each link in the chain, vulnerabilities increase. As objects such as “smart thermostats” and “smart refrigerators” exchange information about our habits, they generate analytics and learn our preferences. Expand these technologies into manufacturing, health care, transportation and energy: both benefits and risks expand exponentially.
Hence the advent of Industry 4.0, defined by Wikipedia as “the current trend of automation and data exchange in manufacturing technologies. It includes cyber-physical systems, the Internet of things and cloud computing. Industry 4.0 creates what has been called a “smart factory.”
In his alarming article on Industryweek.com titled “Cyberthreats Targeting the Factory Floor,” author Barak Perelman (CEO Indegy) warns us “these attacks can cause manufacturing disruptions, leading to defective products, production downtime, physical damage and even threaten lives.”
Manufacturing is now the second most attacked industry behind healthcare. As manufacturers recognize the risks and fortify their systems, securing industrial control systems (ICS) is a tremendous challenge.
Perelman cites IBM X-Force Research’s 2016 Cyber Security Intelligence Index, and The 2016 Manufacturing Report by professional services firm Sikich for statistics on the increase in attacks and which industries are the favored targets.
Ultimately, any environment where cybersecurity is not a priority will be vulnerable. It’s vital to examine your systems and your ICS networks to determine your level of exposure, and take steps to ensure greater security. The era of different functions being isolated from one another is coming to a close, so while we enjoy the benefits of a smart connected infrastructure, we must also recognize the risks.
Other highlights of the Industry Week article:
- “The Sikich report noted that only 33% of the manufacturers it surveyed were performing annual penetration testing within their IT groups. When it comes to ICS networks even less is being done to secure them.”
- “Unlike IT networks, operational networks offer poor or non-existent visibility into ICS and specifically the industrial controllers, which automate industrial processes and manage industrial equipment (I/Os).”
- “Due to the design of ICS networks and the lack of basic security controls such as authentication and encryption, most ICS attacks do not need to exploit software vulnerabilities. Once the network is breached, the attacker gains unfettered access to all the controllers and can alter their configuration, logic and state to cause disruptions.”
- “One of the biggest security challenges manufacturers face is dealing with the variety of different communication protocols used in ICS networks.”
- “Gaining visibility into ICS networks is the first step in being able to protect them from cyber threats. Discovering all assets, especially industrial controllers, is critical. This includes maintaining a reliable inventory of configurations, logic, code and firmware versions for each controller.”
You’re urged to read the entire article, get familiar with the studies cited, and take a close look at your internal practices. In general, the smarter the system, the greater the vulnerability, so it pays to educate yourself and possibly engage a cybersecurity expert to perform penetration testing and craft a security plan.